Computer and Mobile Based Social Engineering
Computer-Based Social Engineering: Hoax Letters: These are fake emails sending warnings about malware, virus and worms causing harm ...
Read moreSocial Engineering and its Attacks
Introduction Social engineering is the art of convincing people to reveal confidential information. By taking advantage of, basic hum...
Read moreSession Hijacking and its Types
Introduction Session hijacking is defined as taking over an active TCP/IP communication session without the user’s permission. When impl...
Read moreSniffing and its Types | Ethical Hacking
What is sniffing? Sniffing is a process of monitoring and capturing all data packets passing through given network. Sniffers are used...
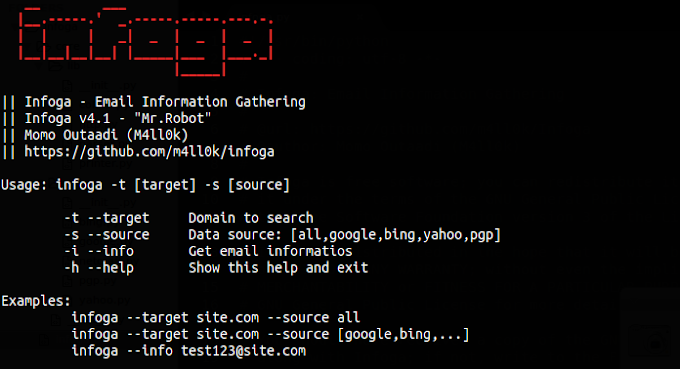
Read moreBEST HACKING TOOLS
1-Nmap-Network Mapper is popular and free open source hacker's tool.It is mainly used for discovery and security auditing.It is used...
Read moreUSE OF FOOTPRITING AND INFORMATION GATHERING IN HACKING
WHAT IS FOOTPRITING AND INFORMATION GATHERING IN HACKING? Footpriting is the technique used for gathering information about computer syst...
Read more6 Interesting Smartphone Trends to Look Out for in 2019
2018 has been an amazing year for smartphones. We saw a lot of new technological advancements emerge this year. Features such as AI, AR,...
Read more7 Mind Blowing Smartphone Hacks
Pricekart.com Today, smartphones have gone to an advanced extent than ever. A new technology will be introduced someday and it will be t...
Read moreINFORMATION GATHERING THROUGH GOOGLE SEARCH ENGINE
Information gathering can be done using technical and nontechnical methods. Technical methods rely on computer-aided techniques for ...
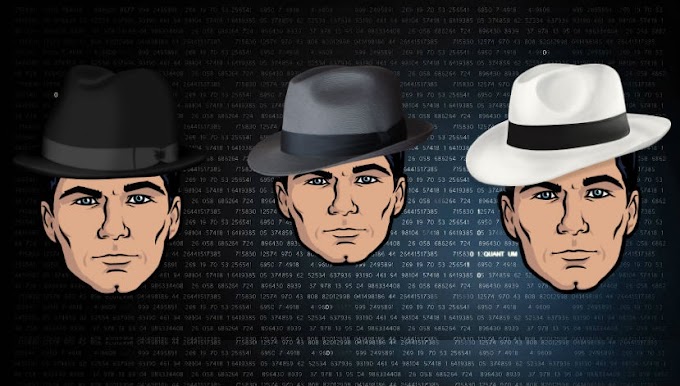
Read moreExplained: What Are White Hat, Gray Hat, and Black Hat Hackers?
Explained: What Are White Hat, Gray Hat, and Black Hat Hackers? Explained: What Are White Hat, Gray Hat, and Black Hat Hackers? ...
Read morePopular Posts
Free Hosting websites

5 free ways to clean up Windows

Why "C" is the default partition on windows.

How to Block YouTube Video Channels
16 Best Whiteboard Animation Software
Categories
- Applications (5)
- Artificial intelligence (5)
- Computer (6)
- Cryptocurrency (4)
- CSS (5)
- Data Science (1)
- Database (2)
- django (2)
- E Commerce (1)
- Ethical Hacking (24)
- Google (5)
- Google Map (5)
- HTML5 (1)
- Instagram (5)
- Internet (40)
- Laravel (24)
- PHP (18)
- python (4)
- social media (14)
- Software (10)
- SQL (27)
- SQL Injection (3)
- stackoverflow (5)
- Technology (27)
- Tutorials (27)
- Web development (24)
- Web Tricks (18)
- window 10 (14)
- Windows (29)
Tags
- 12 factor
- 12 factor app
- 5G
- Adnroid
- AI
- AI Tools
- Android
- android hacking
- Applications
- Artificial intelligence
- babel
- Bitcoin
- Blockchain
- Blogging
- Bootstrap
- c#
- Cloud
- Computer
- Cryptocurrency
- CSS
- Data Science
- Database
- Devin
- Devin AI
- Digmine
- django
- Docker
- E Commerce
- Error
- Ethical Hacking
- Express JS
- frameworks
- Free tools
- Gadgets
- Git
- Google Map
- Hosting
- How to
- HTML
- HTML5
- IDE
- Internet
- Iphone hacking
- javascript
- js
- Laptop
- Laracon
- LaraconIn
- Laravel
- laravel 5
- laravel 6
- Laravel 9
- Laravel Comments
- Laravel Events
- laravel tags
- Laravelista comments
- Linux
- localisation
- Machine learning
- Malware
- Operating System
- partition
- Phone
- PHP
- Processor
- python
- Ripple
- script
- Security
- SEO
- Servers
- shell script
- shell scripting
- short cuts
- Social
- social media
- Software
- software development
- Spam
- SQL
- SQL Injection
- stackoverflow
- Sublime
- Technology
- Tik-tok
- TOP
- Tricks
- Tutorials
- Virus
- vue js
- walmart
- Web development
- Web Tricks
- webdesign
- Webpack
- Website
- window 10
- Windows
- windows phone hacking
- youtube
Recent Posts
Tags
- Android (3)
- Artificial intelligence (5)
- Computer (6)
- Cryptocurrency (4)
- Data Science (1)
- Database (2)
- Git (4)
- Google (5)
- How to (67)
- HTML5 (1)
- Internet (40)
- Laravel (24)
- Linux (5)
- PHP (18)
- python (4)
- short cuts (1)
- Social (17)
- social media (14)
- Technology (27)
- Tricks (14)
- Tutorials (27)
- Website (28)
- Windows (29)