Computer-Based Social Engineering:
Hoax Letters: These are fake emails sending warnings about malware, virus and worms causing harm to the computers.
Chain letters: Asking people to forward emails or messages for money.
Spam Messages: These are unwanted irrelevant emails trying to gather information about users.
Instant Chat messengers: Gathering personal information from a single user by chatting with them.
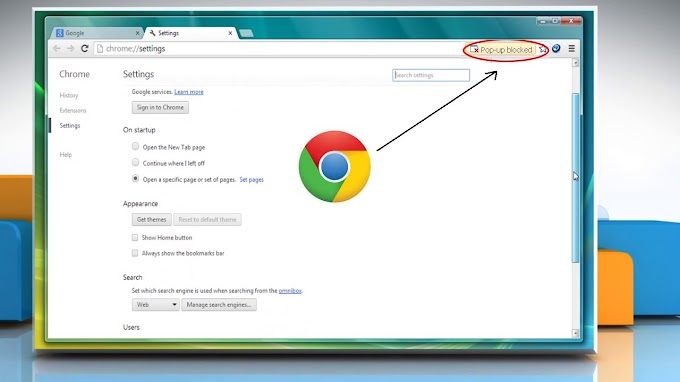
Phishing: Creating a cloned fake website trying to gather sensitive information about users. It can be done by sending a fake email as though coming from an original website and then trying to collect confidential information.
Phishing can also be executed through fake mobile applications.
Mobile based Attacks:
SMS based: Sending a fake SMS saying that the user has won a bounty, urging him/her to register with confidential information or try and collect other important details.
Through Malicious Apps: Applications downloaded from third party sources may be malicious; they can access authentication information and other sensitive details.
Through Email and messengers: Attackers can send spam emails or malicious links through messenger applications. When the victim clicks on it- he may be redirected to a malicious site, or a malware could be downloaded or it may lead to some other malicious activity.
Social engineering on corporate side:
Find an insider: It can be a disgruntled employee who may be the target.
Develop relationship: Develop a friendship with this person and maintain this relationship to the point he trusts you.
Exploit the relationship: Extract the information about the company and other sensitive information exploiting the trust that he placed in you.
Insider Attacks:
An insider attack is very difficult to detect. If a disgruntled employee wants to take revenge; he can install malicious applications to steal/modify information, causing significant damage to the organization or he can be bribed by the competitor to reveal or steal company secrets, intellectual property information, etc.
Countermeasures:
- Educating the employees about the security policies and frameworks, best practices, etc.
- Creating awareness among the users and employees about social engineering attacks.
- Enforcing strict perimeter policy, authentication mechanisms.
- Coming up with effective security policies.
- Enforcing proper access privileges.
- Classifying information and protecting access to them.
- Using Updated antivirus, anti-phishing tools.
- Monitoring and auditing.




0 Comments
Thanks for comment.